Live STIX 2.1 Threat Intelligence Visualizer
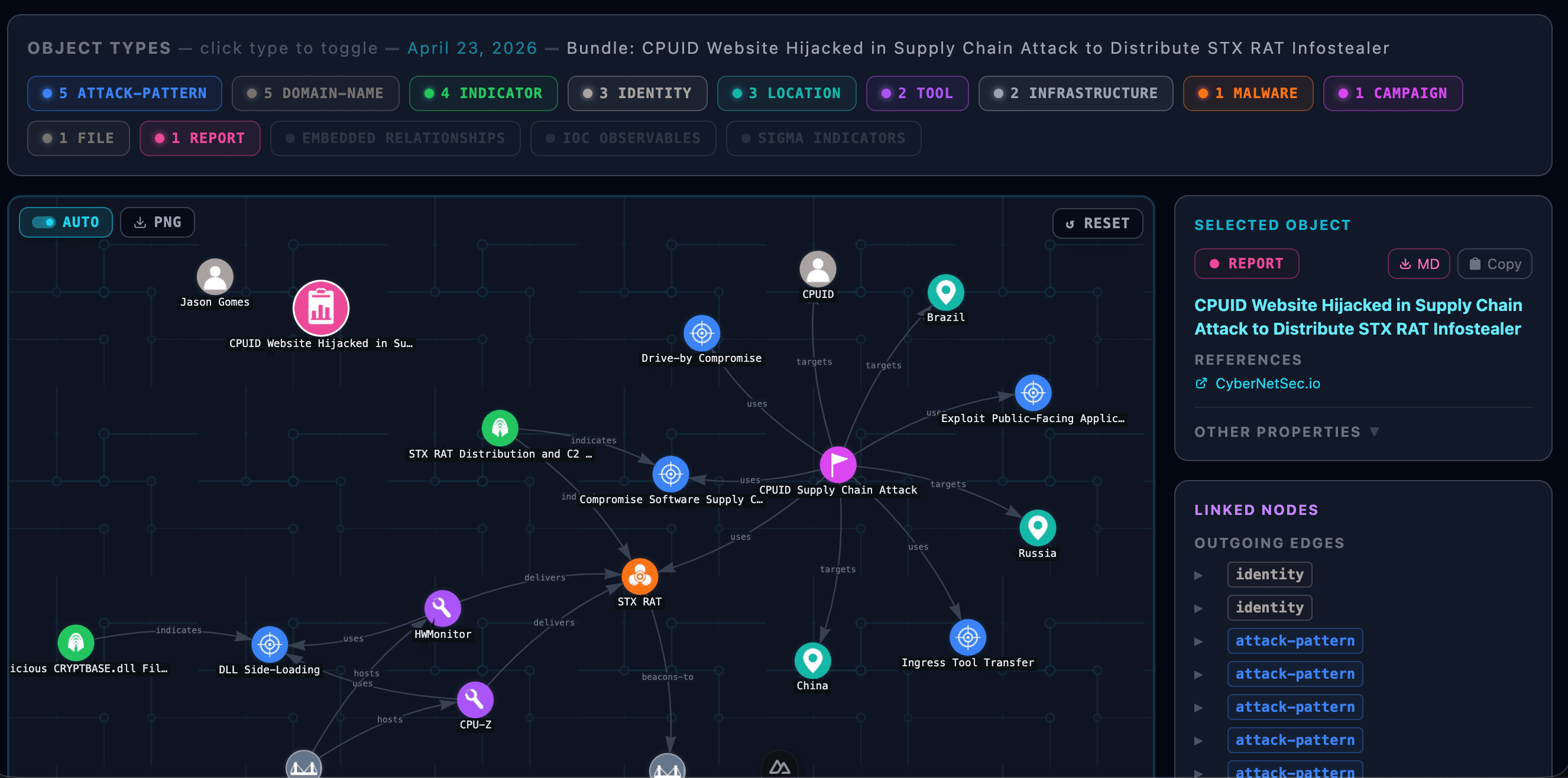
CyberNetSec.io threat briefings rated Critical, High, or Medium severity are backed by a machine-readable STIX 2.1 bundle — structured intelligence you can graph, filter, and export. The visualizer renders the full threat picture: actors, malware, attack patterns, indicators, vulnerabilities, and the relationships that connect them, all in a live interactive force graph. Low and Informational articles typically lack the detailed cyber observables, tactics, and techniques needed to produce meaningful STIX objects.
Look for the View STIX Graph button on any article page to open its bundle directly in this visualizer. Hover or click any node to inspect its full STIX properties. Export to PNG or download the raw STIX 2.1 JSON or SIGMA rules.
STIX bundles are generated for Critical, High, and Medium severity articles published from 1 April 2026 onwards.
Interactive Graph
Force-directed vis-network graph with circuit-board aesthetic. Pan, zoom, and click any node or edge to inspect STIX properties. Hover a type badge to highlight all matching nodes and connected edges instantly.
MITRE + SIGMA
Attack patterns are mapped to MITRE ATT&CK technique IDs. Indicators carry embedded SIGMA detection rules — download them per-indicator or as a bulk YAML file ready to drop into your SIEM.
Article Bundles
Articles rated Critical, High, or Medium severity generate a STIX 2.1 bundle automatically. Low and Informational articles are excluded as they typically lack actionable threat observables. Articles that include a bundle show a View STIX Graph button that opens the visualizer in a new tab — zero copy-paste required.
Sample bundle
CPUID Supply Chain Attack Distributes STX RAT Malware
What is STIX 2.1?
Structured Threat Information eXpression (STIX) is an open standard language and serialization format for exchanging cyber threat intelligence — endorsed by OASIS and adopted across the security industry.
STIX 2.1 defines a rich vocabulary of objects — threat actors, malware, attack patterns, indicators, vulnerabilities, and more — plus typed relationships between them, all serialised as JSON. Bundles are distributed via TAXII 2.1 servers for machine-to-machine sharing.
CyberNetSec.io generates a STIX 2.1 bundle for every Critical, High, and Medium severity article, maps incidents to MITRE ATT&CK techniques, embeds SIGMA detection rules into indicator objects, and publishes everything through a live TAXII 2.1 endpoint. Low and Informational articles are excluded as they seldom contain actionable tactics or techniques.
Common STIX Object Types
Want a new visualisation layout, export format, or STIX object type? Submit a feature request and help shape the roadmap.
Found a rendering issue, broken graph, or missing relationship? Report it via the feedback form and it'll go straight to a GitHub issue.
